WordPress Security in 2020

WordPress is amazing—but just because the software is amazing doesn’t mean we shouldn’t focus on WordPress security.
Because WordPress is open-source, anybody can look at the source code. Hackers and people with malicious intent can analyze every single line of the source code to look for ways to exploit any security vulnerabilities.
WordPress has so many updates because it is constantly patching these issues. For the most part, developers don’t release WordPress updated to add some cool new feature or function; instead, they patch holes in the security.
What happens if you don’t update your WordPress site every time a new security update is released?
You become vulnerable to attacks, which your hosting company can help mitigate. Many attacks are the result of you having specific plugins or a specific combination of plugins installed.
Not every single WordPress install out there is vulnerable. However, developers find exploits regularly: small ones every few days and major ones at least a few times per month. You should be taking steps to secure your WordPress site.
You’ve got nothing to lose by taking these steps, and everything to lose if you don’t take them.
Follow WordPress Security Guidelines
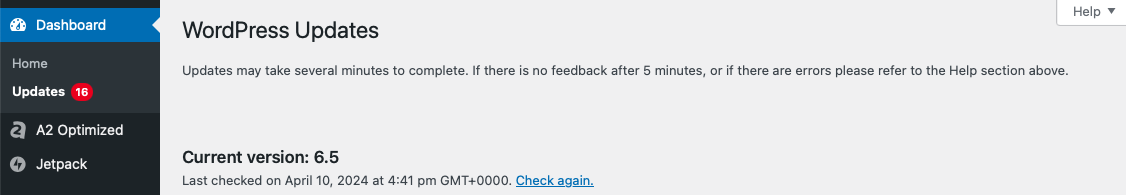
Update WordPress Regularly
You need to update whenever new updates have been released. Again, these updates are plugging up security holes. For example, Reuters is a giant news organization, right? Guess what happened when they didn’t update their WordPress version? You guessed it! Reuters got hacked.
Don’t Use Nulled Plugins and Themes
First, it’s just a jerk move to pirate someone else’s property. Developers put so much time and effort into these projects only to have them stolen. Second, these nulled plugins and themes commonly have been hacked or modified to collect information or otherwise cause harm. Third, if the developer releases a security update, your nulled/hacked copy will not be eligible for the update.
Update Your Plugins and Themes
These need to be updated just as religiously as your core WordPress install does. Security updates are sent out for a reason. You can’t take advantage of these fixes if you’re not actively updating everything.
Use Safe Credentials
Don’t create a password for wp-admin that’s going to be easy to remember. That makes it easy for hackers to guess as well. Don’t use a password that you use elsewhere on the web. If someone hacks your Reddit account or your Facebook account, will they now have your wp-admin password as well?
Use Secure WordPress Security Hosting
Earlier we said that your hosting company can mitigate a majority of WordPress attacks. This is only true if you’re using a company that knows what they’re doing. If you are running WordPress on your own VPN or dedicated server, do you have the technical knowledge to properly handle web-server security?
Multiple layers of both software- and hardware-level security need to be in place in order to ensure your WordPress site can defend itself against any potential attacks. WordPress servers need to be running the latest operating system and security software, constantly scanned for malware and other vulnerabilities, and updated with server-level firewalls.
Many of the top hosting companies out there offer WordPress-specific packages, such as HostGator, Bluehost, and Dreamhost. Still, you may want to check out the WordPress hosting recommendations.
Secure Your wp-admin
Aside from finding exploits and vulnerabilities, the wp-admin section is another weak point popular among hackers looking to do some damage. If you can make it more difficult for hackers and people with malicious intent to find these weak points you are much less likely to get hit.
Unless someone is specifically trying to target you or your site personally, hackers will want to move on to easier targets. Here’s a couple of ways to make sure you’re not an easy target:
Change Your wp-admin URL
Have you ever wondered whether or not a site was running WordPress and typed in the name of the domain /wp-admin/ so that you were brought straight to their admin login page? It makes you stop and think, “Huh…That was easy. If I were a hacker this would’ve been way too easy!” A free plugin like WPS Hide Login will let you change your wp-admin URL to something that can be a bit more tricky for hackers to uncover.
Limit wp-admin Login Attempts
Hackers oftentimes use what is known as a Brute Force method whereby they have software or scripts to try hundreds of thousands of combinations of usernames and passwords until they find the correct combination. By limiting the login attempts you can help prevent this type of acceptance. The free Cerber WordPress plugin is a great way to limit these login attempts.
Don’t Use the Default Admin Username
Hackers need both your username and your password if they want to successfully log into your wp-admin without using any exploits or backdoors. Can you guess what username they’re going to try first? “Admin,” because that’s the default administrator username!
Think about thieves going around checking for unlocked car doors. Sure, they can bust the window open, but they don’t need to when someone leaves their door unlocked. Keeping “admin” as your wp-admin username and not hiding the wp-admin URL is essentially the same as leaving your car doors unlocked. Remember to lock your car doors!
WordPress Dual Factor Authentication
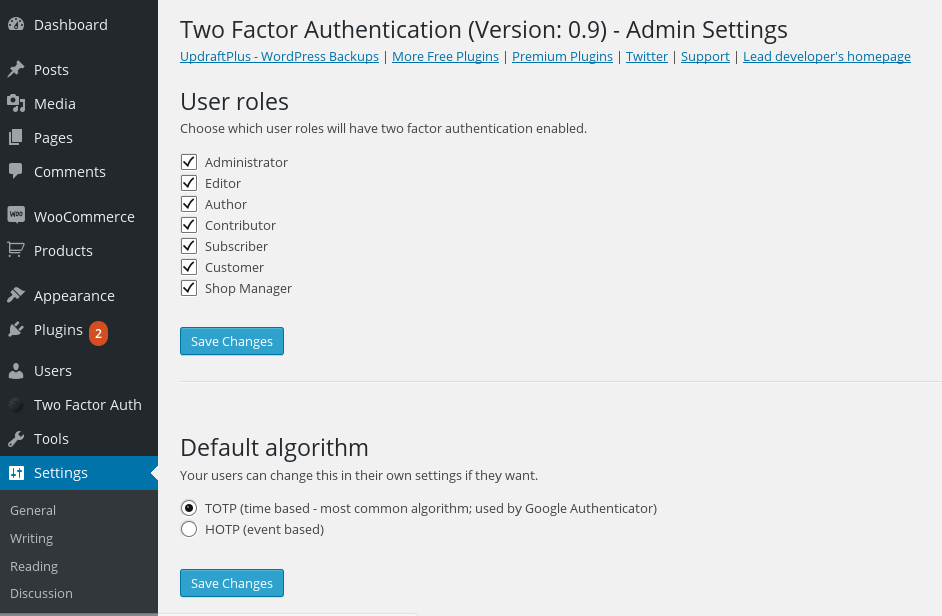
Unless you’ve been living under a rock, or you just avoid doing anything financially related online, then you’ve probably had experience with dual-factor authentication. The first factor comes from you entering your user credentials into a login form. The second factor comes from a source outside of the web page, like a text message, for example, adding an extra layer of security.
So how do we set up a WordPress admin login to have dual-factor authentication? Well, with a plugin, of course! The plugins below will add a third field on your wp-admin login page for you to enter the security code you receive. They also have corresponding apps, like the Google Authenticator or Duo Mobile apps.
Dual-Factor WordPress Plugins:
Use SSL Certificates (HTTPS)

This is one of those tips that applies to every website on the Internet—everybody should be using SSL (secure sockets layer). If you are running a WordPress site that has multiple users, multiple authors, or any e-commerce capabilities you need to use HTTPS!
When you use an SSL certificate, not only do you get a cool S after the HTTP in your URL and a fancy miniature lock icon in the address bar, but you ensure that nothing ever passes from your WordPress install as plain text.
Hackers can intercept these signals that your WordPress install sends through your hosting companies and redirect them to someone else’s web browser or a third-party service like your credit card processor.
Aside from the obvious security, you know what else HTTPS can give you?
- SEO – Google has officially admitted that HTTPS is a ranking factor for their search engine results pages. Your page will rank higher if you’re using an SSL certificate to get an HTTPS URL.
- Trust WordPress Security– Almost 1/3 of visitors know to look for that tiny little lock icon, the green security indicator, or the S in HTTPS. More people are learning every day to look out for these signs of a secure connection. Visitors will be 77% more likely to purchase something from you or subscribe for something if you give them a secure connection.
TL;DR, Get an SSL Certificate. This is one of the most important aspects of web security. Go ahead, minimize this web page and go install one.
Is Your wp-config.php Secure?
Those of us old-school WordPress users know how vital that wp-config file is to WordPress security, installation, and overall usage. But, because the installation process has become so easy, new WordPress users may not even know it exists.
The wp-config.php file contains a lot of important and potentially vulnerable information, like your MySQL database credentials. Wp-config.php is the single most important file when it comes to WordPress security. So, how can you make it secure?
Move the wp-config.php File
By default, you can find this file in the root directory of your WordPress install, usually in the public_html folder. Consider moving it. Here’s an amazing explanation by Aaron Adams on how to move the wp-config.php file.
Wp-config.php CHMOD Permissions
When WordPress gets installed manually, the documentation suggests you change the permissions of this file to 400 or 440 to prevent any other users on the server from reading it, accessing it, or changing it. You can do this by right-clicking on the file and finding Permissions or CHMOD. You may need to check with your web hosting provider.
WordPress Is 100% Safe To Use
Any application on the web is going to open itself up to hackers looking to take advantage of any weakness that they can find. WordPress is no exception to this rule. We know we have listed a lot of steps you should take in order to secure your WordPress install, but that doesn’t mean WordPress isn’t safe to use. It just may take some tweaks to ensure you’re as unhackable as possible.

Comments